There is an illustration from the webcomic xkcd (number 2347) that frequently circulates in engineering forums and corporate Slack channels. At first glance, it is a visual joke about software dependencies. In practice, it is the most accurate architectural diagram of the modern digital economy.
The image shows a colossal castle of stacked blocks, labeled “All modern digital infrastructure”. This structure, which represents everything from global financial systems to cloud infrastructure, balances precariously on a single, tiny pillar at its base: “A project some random person in Nebraska has been thanklessly maintaining since 2003”.
For years, we engineers laughed at this comic with some discomfort. We knew it was true. However, it wasn’t until recently that the entire industry experienced a chill watching how that prediction almost caused one of the greatest cybersecurity collapses in internet history.
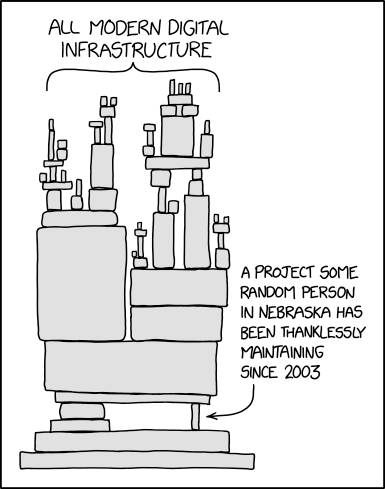
Original illustration by Randall Munroe (xkcd.com/2347)
Table of contents
Open Table of contents
The Tragedy of the Commons in Open Source
Today’s development ecosystem is a triumph of human collaboration. When we initialize a project, we don’t write data compression algorithms or encryption protocols from scratch; we delegate that responsibility to Open Source libraries.
This model has democratized and accelerated innovation, but it has hidden a severe structural problem: the asymmetry of extracted value versus returned value. Multi-trillion dollar corporations build their commercial products on the unpaid work of thousands of independent developers who maintain the code in their spare time.
When that “person in Nebraska” gets exhausted, suffers from burnout, or simply changes interests, the foundational block of the tower begins to crack. And it is exactly in these cracks where modern threats operate.
The xz-utils Case: The Nightmare Made Real
To understand the gravity of this structural fragility, we must analyze the incident of xz-utils (CVE-2024-3094), an event that redefined our understanding of supply chain attacks.
The Target: An invisible pillar
xz-utils is a ubiquitous data compression utility in Linux and Unix-based operating systems. It is such a low-level component that the vast majority of developers never interact directly with it, but upon which critical operating system processes depend.
The creator and lead maintainer, Lasse Collin, had been maintaining the project for years. Like many solo maintainers, Collin faced constant pressure, mental health issues, and the natural wear and tear of dealing with unpaid demands from a global user base.
Long-Term Social Engineering
In late 2021, a user under the pseudonym “Jia Tan” began contributing to the project. Unlike a brute force attack, this was a meticulous intelligence operation that lasted years.
Jia Tan started by submitting useful and legitimate patches. Simultaneously, other fake accounts (or sockpuppets) began pressuring Collin in public forums, complaining about the slowness in code review and demanding that more control be given to other developers. Vulnerable and exhausted, Collin gave in. Gradually, Jia Tan gained co-maintainer permissions and eventually almost total control over the repository.
The Payload
Once in control, Jia Tan introduced a backdoor of terrifying technical sophistication. The malicious code was not obviously in the main GitHub repository, but hidden inside seemingly harmless binary test files. During the build process, a highly obfuscated script extracted and executed the malicious code, injecting it directly into OpenSSH (the standard protocol for accessing servers remotely).
The ultimate goal was to allow the attackers to execute arbitrary code with administrator privileges on virtually any modern Linux server in the world, leaving no trace in the logs.
Saved by 500 milliseconds
The attack came close to being integrated into the stable releases of major distributions like Debian and Red Hat. Global disaster was averted by pure chance.
Andres Freund, a Microsoft engineer, was performing micro-optimizations on a Debian system when he noticed that SSH processes were consuming an unusual amount of CPU and taking approximately 500 milliseconds longer than normal to complete.
His professional curiosity led him to investigate that half-second of latency. Pulling the thread, Freund unraveled the conspiracy, discovered the backdoor, and alerted the world just weeks before the malicious update was distributed globally.
The Structural Lesson
The xz-utils case proved that the most imminent threat to our digital infrastructure is not necessarily a cryptographic vulnerability, but the systemic exploitation of the human factor in open source.
We cannot rely on a meticulous engineer noticing a 500-millisecond delay to save the internet. The solution requires a paradigm shift at the corporate and institutional level:
- Supply Chain Auditing (SBOM): Organizations must implement strict Software Bill of Materials, knowing exactly what projects they depend on and who maintains them.
- Institutional Funding: Multi-billion dollar companies must treat Open Source project sponsorship not as charity, but as a critical infrastructure operating expense. Paying for the maintenance of base libraries is as essential as paying the AWS bill.
- Maintainer Support: We must rethink how key projects are managed, ensuring that critical infrastructure components do not depend on a single unpaid individual.
The digital tower we inhabit is a miracle of modern engineering, but it is still a glass structure. Until the industry acknowledges and remunerates the invisible effort that sustains the base, we will continue to be at the mercy of the fragility of the Nebraska pillar.